Lock
Background
Locks have been used to fasten doors against thieves since earliest times. The Old Testament contains several references to locks, and the first archaeological evidence of locks are about 4,000 years old. These are Egyptian locks depicted in the pyramids. These earliest locks were of a type known as pin tumbler, and they are actually not very different from common door locks in use today. The Egyptian lock consisted of a heavy wooden housing mounted to the door. A wooden bolt passed through the lock and was held in place by iron pins which dropped into slots and held it firm. The key was a straight piece of wood with pegs projecting up from its end. When the key was inserted and pushed upwards, the pegs on the key lifted the pins in the lock, and the bolt was freed.
The Greeks developed a simple door lock by about 700 B.C. This used a latchstring to pull a bolt through brackets in the door. By pulling the string, the homeowner could lock the door from the outside. Then, the string was stuffed back through the keyhole. The key itself was a sickle-shaped piece of metal from two to three feet long. The key could be fitted into the hole in the lock to pull back the bolt from the outside. The major drawback to this lock was that anyone with a curved stick or their own key could open it. And, the large metal key was cumbersome.
Romans adopted the Greek lock system, but solved the problem of the heavy key by chaining it to a slave, and then chaining the slave to the doorpost. Eventually, Romans developed a new kind of lock, called the warded lock. In the warded lock, notches and grooves called wards were cut into the keyhole, and the key was cut with corresponding notches and grooves. Only the proper key could fit into the keyhole, and then its tip engaged the bolt and withdrew it. The warded lock was much smaller than its predecessor, and keys were small enough that no slave was needed to take care of it. But because the classic Roman toga had no pockets, the key still wasn't easy to carry, and so it was usually attached to a finger ring. Warded locks were widespread in Europe by the thirteenth century and remained in use well into the eighteenth century. They persisted in spite of the fact that they were easy to pick, and were barely an obstacle to determined thieves.
The Romans also used padlocks, in which a key turned a bolt releasing a spring on a shackle. These were used for locking trunks. Similar locks were invented in China, India and Russia during the same era. The Chinese also invented the combination lock. It had moveable rings inscribed with numbers or letters, and its hasp was released only when the rings were aligned in the proper sequence of symbols. Combination locks found their way to Europe, and were used in the Middle Ages especially on couriers' dispatch boxes.
European locksmiths in the Middle Ages made beautiful, intricate locks which took appallingly long hours of work to build and offered little real security. Locksmiths apprenticed for 10 years to reach the journeyman level. To reach the rank of master, the locksmith had to complete a masterpiece lock for approval by his guild. These masterpieces took thousands of hours to complete, and the results were generally much more decorative than functional. Locks that offered improved protection against theft were not developed until the late eighteenth century, when an English locksmith, Robert Barron, patented what was known as the double-action lever-tumbler lock in 1788. Barron's lock had two interior levers held by a spring. These levers, or tumblers, had notches that hooked over the bolt and held it shut. The key also had notches on it corresponding to the notches on the levers. When the right key was inserted, it would lift both tumblers, and the bolt could be drawn. Other inventors added many more tumblers to this design, and it proved much more difficult to pick than the earlier warded locks.
Linus Yale Jr., an American locksmith born in 1821, made a significant improvement in lock design in 1861 with his invention of the modern pin-tumbler lock. The design principal was similar to the Egyptian lock. This lock has a rotating cylinder which is held fast in the bolt by a series of five spring-driven pins of different heights. The key has five notches on it that correspond to the heights of the five pins. When the correct key is inserted, the pins line up level, and the cylinder can be turned to disengage the bolt. If the wrong key is inserted, the pins catch. Picking a Yale lock proved extremely difficult, and the parts for the lock could be inexpensively mass-produced by machine. Within several years of its invention, the Yale lock became the standard, replacing virtually all earlier lock technology.
Even more sophisticated locks were developed in the twentieth century, including timer locks used in bank vaults, push button locks, and electronic locks that operate with a credit card like key. The manufacturing process that follows is for a standard pin-tumbler lock. This is the kind of lock that may be found on any front door or file cabinet drawer.
Raw Materials
Standard five-tumbler key locks are made of various strong metals. The internal mechanisms of locks are generally made of brass or die-cast zinc. The cam, which is the tongue that protrudes from the lock to secure it, is usually made of steel or stainless steel. The outer casing of a lock may be made of brass, chrome, steel, nickel or any other durable metal or alloy.
The Manufacturing
Process
Design
-
1 Locks come in grades, from low-security to high-security. A
low-security lock is generally made from cheaper materials, and its
parts can be mass-produced. A company that manufactures low-security
locks may have two or three available models, and keep in stock the
parts needed to customize them. Beyond low-security, the lock
manufacturer is generally what is called an original equipment
manufacturer, meaning that they make the parts for their locks as well
as the final products. This kind of manufacturer may keep only the most
basic and common parts in stock, and most of its orders require custom
design.
The process begins with the manufacturer assessing the customer's specifications. The customer orders a lock to fit a certain size door for example, and asks that the locks can be opened with a master key. The lock manufacturer then comes up with the best design for that customer's needs. In some cases, a customer may have purchased locks in the past from one company, and now wants more identical locks from a different manufacturer, who promises to make them more economically. Then, the lock manufacturer examines the customer's original locks and goes through what is known as a reverse engineering process. The manufacturer's design team figures out from the existing lock how to make their product match it. In many cases, the customer's first lock company has patented aspects of its lock construction. The second manufacturer may not duplicate it without infringing the other company's patents. So, the designers "design around" the first company's product, producing a lock that will match the customer's originals and serve the same purpose, but using different mechanisms. Medium and high security locks in most cases go through this design stage, making the production of locks a time-consuming process. A reputable manufacturer making anything but low security locks may take from eight to 12 weeks to produce locks for an order, from the time the specifications are given to when the locks are packed and shipped.
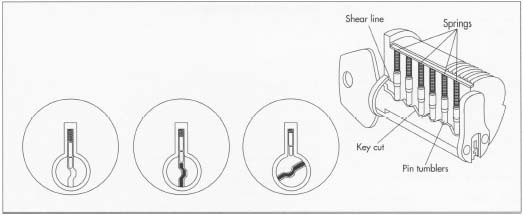 A cutaway of a standard Yale lock. This lock has a rotating cylinder that is held fast in the bolt by a series of five spring-driven pins of different heights. The key has five notches on it that correspond to the heights of the five pins. When the correct key is inserted, the pins line up level, and the cylinder can be turned to disengage the bolt. If the wrong key is inserted, the pins catch.
A cutaway of a standard Yale lock. This lock has a rotating cylinder that is held fast in the bolt by a series of five spring-driven pins of different heights. The key has five notches on it that correspond to the heights of the five pins. When the correct key is inserted, the pins line up level, and the cylinder can be turned to disengage the bolt. If the wrong key is inserted, the pins catch.
The key
- 2 For the standard five-tumbler key lock, the key is made first. The lock manufacturer buys key blanks and cuts the ridges, or combinations, in each key. Each key has five bumps on it that are cut to different levels. These levels are designated by numbers. A low cut is one, next up is two, then three. In many cases, there are only four levels, though some manufacturers may use as many as seven. A five-tumbler key lock with four levels in the key yields four to the fifth power, or 1024, different possible combinations of ridges in the key. The five ridges are listed by the height of each level, yielding what is called the combination for the key. A key with the combination 12341 is cut with the first ridge at level one, the second at two, the next at three, and so on. The lock manufacturer chooses the combinations from a random list and cuts each key differently.
Internal mechanisms
- 3 The internal mechanisms are made next. These have been designed to fit this particular lock order, and the machinery that makes them may have to be re-tooled or reset. Because the tiny interior parts, specifically the pins, must be manufactured to exceedingly fine tolerances, the machinists may make a trial run before starting a big job. Then the machines may be re-set if necessary. The machining of small brass parts takes many steps. They may be cast, then grooved, ridged, jeweled, and polished. Precision tools handle these jobs, cutting the metal to within tolerances of plus or minus 0.001 of an inch.
Other parts
- 4 The manufacturer also makes the other parts of the lock. The cylinder, or plug, that the key fits into, guard plates, washers, the bolt or cam, and the casing, are all made according to design specifications, by die-casting and then further machining. The number of parts varies with the design of the lock, but even a small and relatively simple lock may have thirty separate parts, and some of these parts require multiple toolings. The process of making the lock components can take several weeks.
Assembly
-
5 When all the parts are ready, the locks are assembled by hand. Lock
workers sit at well-lit tables with a kit of the pieces of the lock in a
bin, and the key on a stand in front of them. An experienced worker can
tell the combination of the key just by looking at it. The worker first
fills the plug, or cylinder, of the lock with the pins that correspond
to the combination of the key. The worker inserts a tiny spring and then
the lock pin, using a small tool called an assembly pick to hold the
small parts. The assembly pick has a small screwdriver on one end and a
point on the other, and the worker uses it to prod the delicate parts in
where they belong. Once the
plug is filled according to the key combination, the worker snaps or screws together the other parts around the lock. Though it is skilled work, it takes no special training, and these workers are not locksmiths.
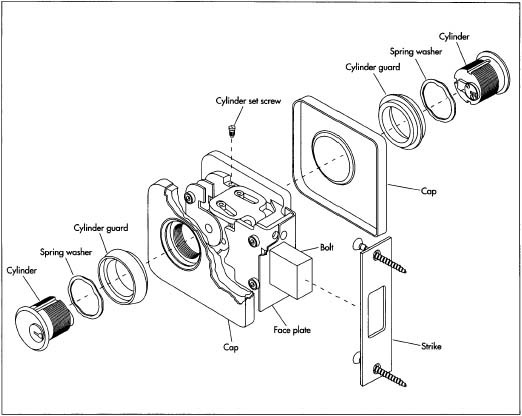 Cross section of a typical lock.
Cross section of a typical lock.
Final steps
- 6 Once a lock is fully assembled, the worker checks it with the key to make sure it works. It may pass to a quality control station at this point, and then be dusted or polished. Workers package the completed locks and box them for shipment.
Quality Control
The most important aspect of quality control in lock manufacturing is ensuring that the tiny machined parts are the exact sizes specified. For a new custom order, the machinists usually produce trial samples of the parts, and each one of these may be inspected and measured manually, using precise gauges. If all seems to be going well, the machinists will run the rest of the order, and then perhaps one of every 500 or 1,000 parts is checked. After the worker assembles the lock, he or she tests it with the key to make sure it works properly. A quality control specialist may also spot check the locks at this stage.
The Future
Many entities such as universities and large corporate headquarters that use large numbers of locks are converting to electronic pass-key systems. These use a magnetic swipe card to open a door. The cards can have a bar code on them, and computers can be used to store information on who goes in through each door, raising privacy issues for some concerned people. Other high-tech locks open with voice activation or palm or fingerprint recognition. Such locks offer relatively high security, but are generally too expensive and elaborate for the ordinary citizen's home. However, the trend towards these kinds of electronic and computer-controlled locks is growing in the late 1990s, and they will undoubtedly be more prevalent in the future.
Where to Learn More
Books
Roper, C.A. The Complete Book of Locks and Locksmithing. Blue Ridge Summit, Pennsylvania: Tab Books, 1991.
Tchudi, Stephen. Lock and Key. New York: Scribner's, 1993.
Periodicals
Belsie, Laurent. "Slide Toward Surveillance Society: New Technology Allows Government and Corporations to Cut Fraud and Boost Security, but Privacy Concerns Mount." Christian Science Monitor. (March 4, 1999).
Leigh, Bobbie. "An Alarming Trend: Bulletproof Living." Wall Street Journal. (November 29, 1996).
— Angela Woodward
Comment about this article, ask questions, or add new information about this topic: